

None of this has anything to do with root on my machine though.
But it does. If your machine is compromised, and they have root permissions to run whatever they want, it doesn’t matter how segmented everything is, you said yourself you jump between them (though rare).
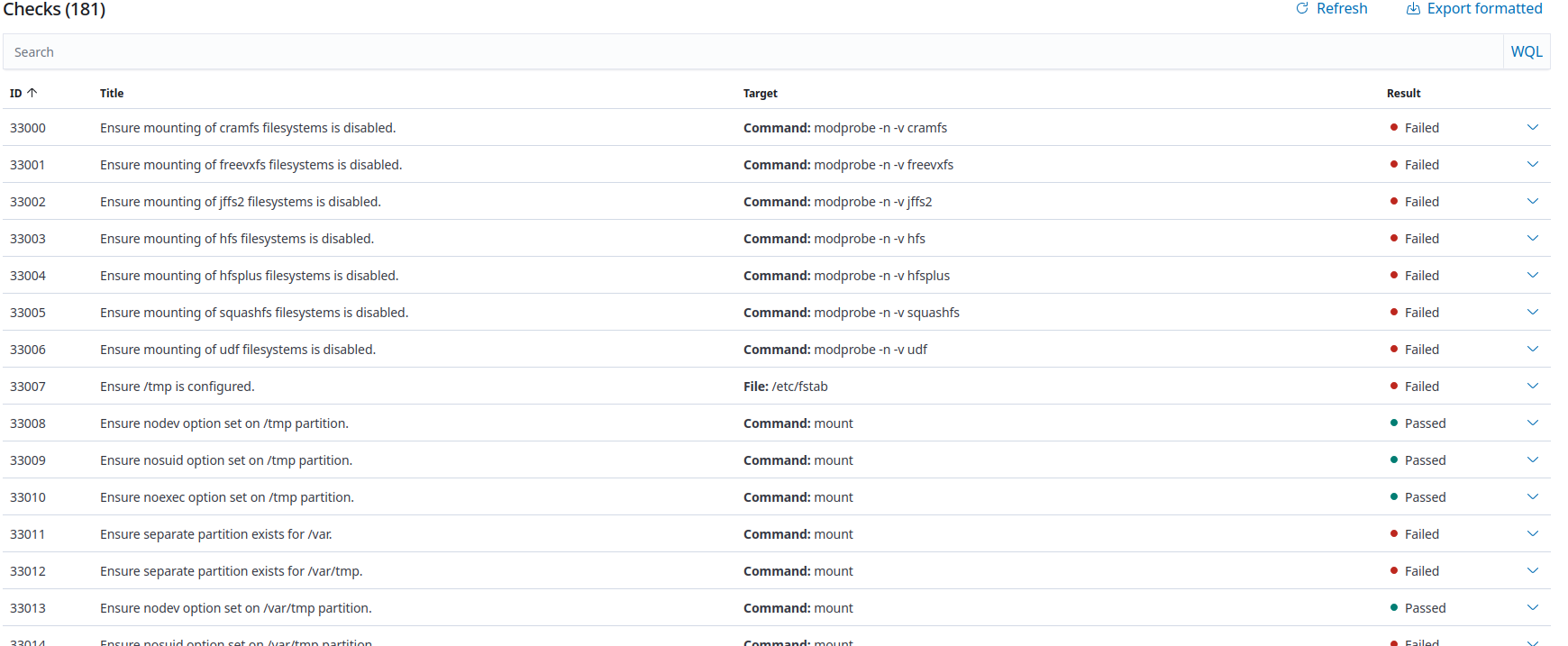
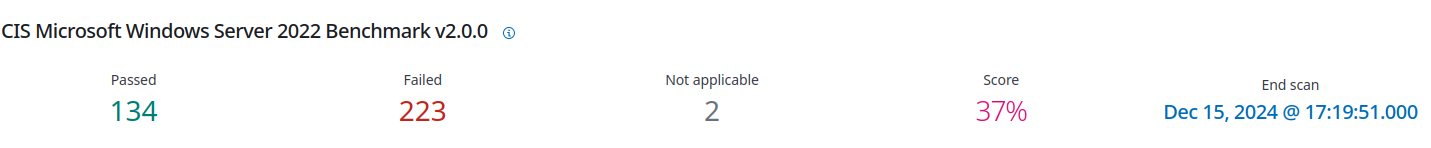
Security Configuration Assessment
SCA is for payment services, no? I’m in the US, and this seems to be an EU thing I’m not very familiar with, but regardless, we don’t touch ecommerce at all, we’re B2B and all payments go through invoices.
No, it’s just a term for a defined check that configurations meet a standard. An SCA can be configured to check on any particular configuration change.
Also, that should be painfully obvious because you wouldn’t get reporting updates, no?
Not necessarily? Hard to tell if something is disabled vs just off.
If you’re worried someone will disable your tools, why would you hire them in the first place?
I don’t hire people… especially people in other departments.
But while I found this discussion fun, I have to get back to work at this point. Shit just came up with a vendor we used for our old archaic code that might accelerate a rust-rewrite… and logically related to the conversation I might be in the market for some rust devs.




He would be fine if he only talked pretentiously in the fields he actually knows stuff about. He’s earned it for astrophysics. But its the everything else…